May 16, 2013
New Virus Attack: Walmart.com Emails
The purpose of this message is to inform you of a new sophisticated Virus infected message, that does not require you to click on links - simply load the message into a "dated" web browser (like Firefox, IE, Chrome, Safari) and it searches for exploits on your computer.
If your system had AVG popup as you viewed it, and it blocked the message - great! That means AVG stopped its actions cold. If it did not, we should have your system inspected. Please contact the IT Support Center at x4225.
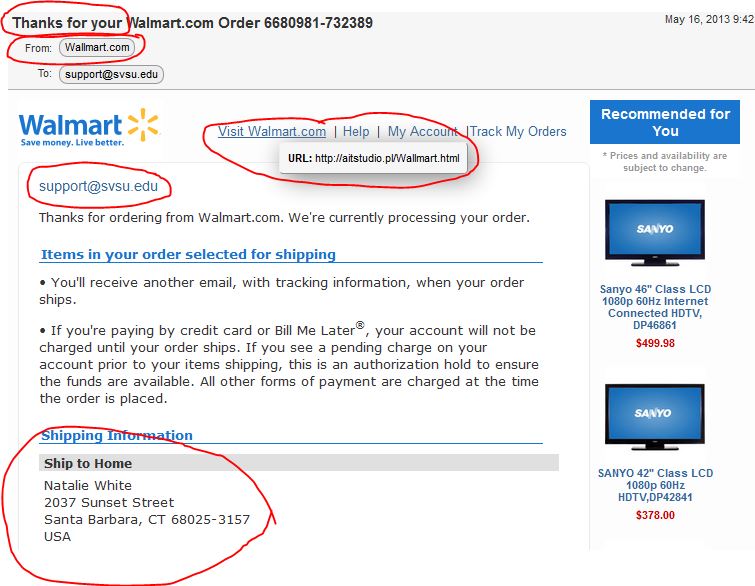
Below is a sample message. The circled areas are items you should scrutinize before acting on messages.
- If you hover over the From address - you'll see not only is Walmart misspelled (has two L's), and the actual address is poorly named and even sometimes has a different extension (.com, .net, .org).
- If you hover over the links (not clicking) it shows a completely different web address not related to the subject or material in the message.
- The fact they use an email address for salutation, versus your actual name on file when you order things online.
- The fact that the shipping details are not even close to being related to you.
Again, being aware of these kinds of nuances in messages will help further protect you. Be careful and assume that the message is not legitimate. Ask yourself basic questions.
- Do I have a Walmart/PayPal/eBay account?
- Did I order something online recently?
- Does something about this message seem suspicious or "phishy"?
And as always, please feel free to contact the IT Support Center (989-964-4225) for advice or to report something that is phishy. If you accidentally clicked and became a victim, you should change your passwords immediately and contact the IT Support Center to have your system inspected.